For other 5.1 deep dives:
- Distributed Virtual Port Group Separation for management domain appliances
That’s a mouthful.
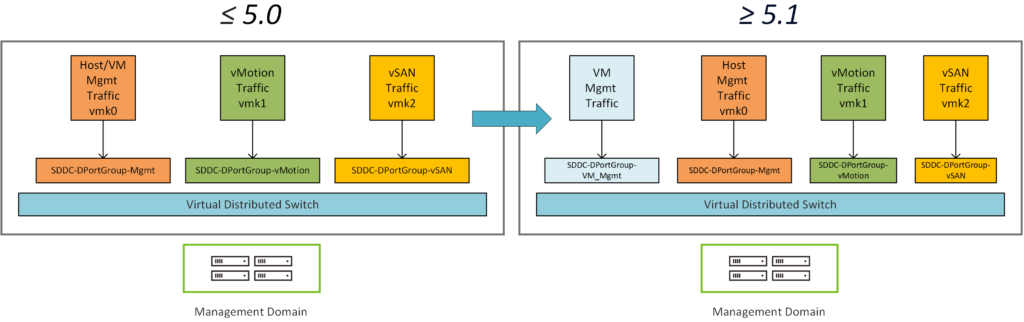
Today, the management components reside on a subnet/vlan that is shared with the management ESXi hosts vmk0 interface. We are changing this.
This feature enables the traffic isolation between management VMs (i.e., SDDC Manager, NSX Managers, vCenter, VxRail Manager & Edge Node VM) and the ESXi Management VMK interface.
During VCF bringup, there is an additional field (VM Management Network) in the deployment spreadsheet to configure this portgroup, it looks like this:
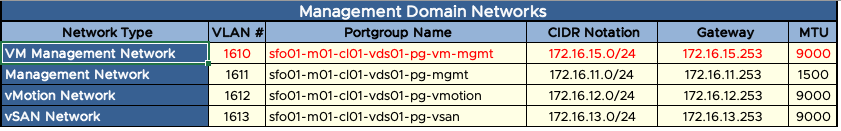
This is also configurable using a json, an additional networkType has been created called VM_MANAGEMENT
If this is not defined, the portgroup will still be created – using the values of the Management Network (ESXi vmk0 portgroup).
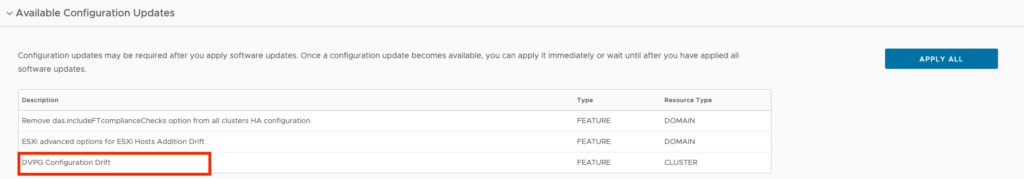
So what about existing deployments upgraded to 5.1?
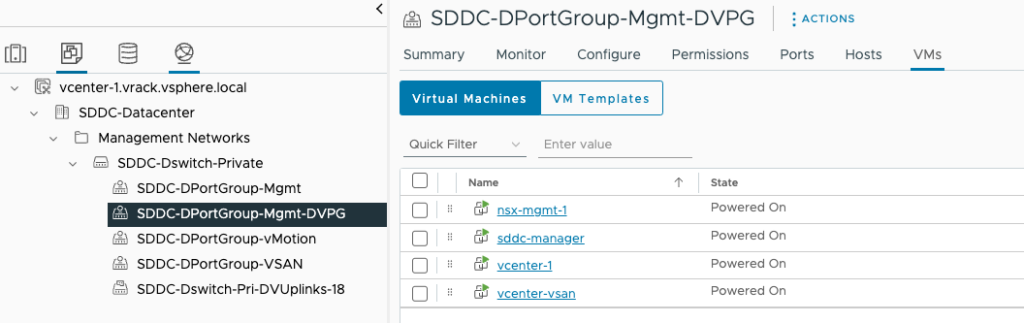
Applying the 5.1 configuration drift will create another distributed portgroup and move all VMs connected to the original Management Portgroup, the information used to create this portgroup is replicated from the existing portgroup. There is no option to change this to a different VLAN/subnet as that would require IP changes, something we do not support. The name of this newly created portgroup will be what the management portgroup is named with the DVPG suffix.
Hi,
during the upgrade from VCF 4.5 to 5.1 we are having error while applying the ESXi configurations. DVPG configuration drift error. May be this is due to the change that has introduce in 5.1. What is way to fix the issue to move forward….
Hi Sudheer,
Sorry for the late reply. Missed this comment.
Were you able to get this resolved? Did you manually rename any portgroups by chance?
Hi Martin,
I am also facing the same error. I didn’t change the port group name. I have 3 workload domain, 1st one is management domain and other 2 is VI workload domain. Management domain DVPG configuration drift applied successfully but other 2 VI workload domain failed with error “VM Migration failed”. When I investigate the issue from vCenter of the respected VI workload domains, I see that port group with “dvpg” suffix is created, settings (VLAN, Teaming) of the original management port group also replicated and edge vms of nsx (As it is VI Workload domain so SDDC Manager, vCenters, NSX Managers are in management domain) also migrated from original management port group but shows error in SDDC Manager.
Note: I upgraded vcf from version 4.5 to 5.2